Top-rated Cybersecurity Solutions
Every 39 seconds, a cyber attack occurs, underscoring the pressing need for robust cybersecurity solutions. From ransomware to phishing scams, the digital landscape is rife with threats that can cripple even the most fortified systems. These attacks not only put sensitive data at risk but also jeopardize the very integrity of businesses globally.
The evolution of cybersecurity solutions has been remarkable over the past few decades. Back in the early days, simple antivirus software was considered adequate. Now, comprehensive solutions like advanced threat protection and AI-driven security measures dominate the market, catching nearly 95% of threats before they cause harm. This shift highlights the critical importance of adaptive and proactive defenses in today’s cyber environment.

Top-rated cybersecurity solutions
Cybersecurity is more important than ever with the rise in online threats. Advanced Threat Protection (ATP) stands out as a top solution. It focuses on preventing, detecting, and responding to threats. ATP uses machine learning to identify suspicious patterns quickly. This technology helps companies stay one step ahead of cybercriminals.
Artificial Intelligence (AI) in cybersecurity has revolutionized protection methods. AI-driven solutions can analyze vast amounts of data efficiently. This helps in identifying potential threats faster than humans. With AI, systems can learn and adapt, improving defense mechanisms over time. It’s like having a virtual security guard watching over your data constantly.
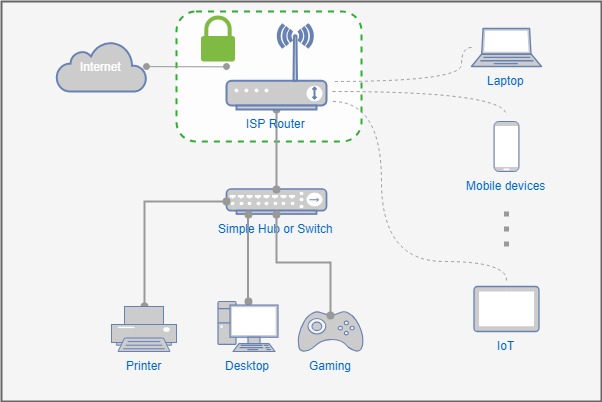
Unified Threat Management (UTM) simplifies complex security processes. It combines several security features into one solution. Features like firewalls, VPNs, and antivirus are integrated to provide a strong shield. Businesses prefer UTM for its simplicity and effectiveness. This approach reduces the need for multiple separate security tools.
Choosing the right cybersecurity solution depends on specific needs. Some might prefer a solution that focuses on preventing attacks, while others prioritize detecting them. Here’s a basic comparison of features:
| Solution | Features |
|---|---|
| ATP | Detection, Response |
| AI-Driven Security | Adaptation, Learning |
| UTM | Simplified Management |
A look at Advanced Threat Protection
Advanced Threat Protection (ATP) is a modern cybersecurity tool that fights against harmful attacks. It works by identifying suspicious activity and stopping threats before they cause harm. ATP uses advanced technologies like machine learning to detect patterns that might indicate an attack. This proactive approach helps in preventing data breaches. Businesses rely on ATP to secure sensitive information from cybercriminals.
ATP solutions are comprehensive and include multiple layers of security. They focus on detecting and responding to various threats such as malware, phishing, and ransomware. Here’s a list of common threats ATP tackles:
- Malware Attacks
- Phishing Scams
- Ransomware
- Zero-day Exploits
One major advantage of ATP is its ability to adapt quickly. As new threats evolve, ATP systems learn and adjust to tackle them. This keeps businesses protected in an ever-changing cyber landscape. By using ATP, companies can ensure they are always prepared for new and advanced threats. It provides peace of mind in knowing their security measures are up-to-date.
Many businesses choose ATP because of its effectiveness and robust protection capabilities. It not only protects data but also helps in maintaining customer trust. Let’s take a closer look at some features offered by ATP systems:
| Feature | Purpose |
|---|---|
| Real-time Monitoring | Continuous Threat Detection |
| Incident Response | Quick Mitigation Steps |
| Threat Intelligence | Up-to-date Information on Threats |
Exploration of AI-Driven cybersecurity
AI-Driven cybersecurity is changing the way we protect our digital world. It uses artificial intelligence to discover threats quickly and efficiently. By analyzing huge amounts of data, AI can detect patterns signaling a potential attack. This capability makes response times much faster than traditional methods. Companies are increasingly adopting AI to strengthen their defenses.
AI systems in cybersecurity can adapt to new threats as they emerge. This flexibility is crucial in defending against ever-evolving cyber threats. AI can learn from past attacks, improving its accuracy over time. Here’s a table showcasing some key benefits of AI-Driven cybersecurity:
| Benefit | Impact |
|---|---|
| Speed | Faster Threat Detection |
| Learning Ability | Improved Accuracy |
| Adaptability | Handles New Threats |
AI is not just about fighting threats but also about predicting them. Predictive capabilities allow security systems to foresee potential vulnerabilities. This proactive approach goes beyond just dealing with existing issues. It helps in preventing attacks before they happen. This makes AI a powerful tool in cybersecurity.
Businesses benefit greatly from AI-driven solutions. These systems save time and reduce risks associated with manual monitoring. Here are some features that make AI-driven cybersecurity attractive:
- Automated Threat Analysis
- Real-time Alerts
- Continuous Monitoring
With such features, organizations can stay more secure with less effort. AI’s role in cybersecurity is poised to grow even further.
The rise of Unified Threat Management
Unified Threat Management (UTM) is becoming a popular choice in cybersecurity for simplifying protection. It brings together multiple security features into one package. This includes firewalls, antivirus, and intrusion detection, all working together. The integration offers a seamless defense mechanism, making it easier for businesses to manage. Companies now have a more streamlined way to protect against various cyber threats.
Before UTM, businesses needed separate systems for each security task. This was both costly and complex. UTM reduces those complexities by offering an all-in-one solution. Here are some benefits of using UTM:
- Cost-Effective
- Simplified Management
- Comprehensive Protection
Adopting UTM also helps in faster decision-making during threats. By having all tools in one place, teams can act quickly to stop attacks. The efficiency gained is a key reason for its rising popularity. With faster responses, the damage from potential threats is minimized. Companies appreciate this straightforward approach to security management.
UTM is not just for large businesses, but also smaller organizations. Its scalability means it can grow with the company. This flexibility makes it an attractive option for businesses of any size. Here is a table showcasing features and their contributions:
| Feature | Contribution |
|---|---|
| Firewall | Blocks Unauthorized Access |
| Antivirus | Detects and Removes Malware |
| Intrusion Detection | Monitors and Alerts on Suspicious Activity |
Such comprehensive security eliminates the need for multiple vendors. This consolidation saves money and reduces complexity. As cyber threats evolve, UTM offers a smart approach by adapting to new challenges. The rise of UTM indicates a future where cybersecurity is more accessible and effective.
Businesses now have a trusted ally in the cybersecurity landscape with UTM. The ease of management and comprehensive coverage encourages its adoption. This unified approach ensures organizations are well-protected against a range of potential threats. Unified Threat Management is a beacon of simplicity amid the complex world of cybersecurity.
How cybersecurity solutions have evolved over time
Cybersecurity solutions have come a long way from their humble beginnings. In the early days, basic antivirus software was all that protected computers. This software was limited and often unable to tackle complex threats. Over time, as the internet became more widespread, so did the types and frequency of attacks. This drove the need for more advanced security measures.
Today, cybersecurity solutions have evolved to include sophisticated tools like firewalls, encryption, and intrusion detection systems. These tools work together to provide comprehensive protection. Each tool targets specific types of threats, ensuring all bases are covered. Here’s a table comparing traditional and modern solutions:
| Solution Type | Key Features |
|---|---|
| Traditional | Basic Antivirus |
| Modern | Advanced Encryption, Firewalls, AI-Driven Systems |
The rise of artificial intelligence has revolutionized cybersecurity. AI-driven tools can analyze data faster and more accurately than humans. This means threats are detected and dealt with almost instantaneously. With AI, systems learn from each encounter, improving over time. This evolution marks a significant shift in how security is managed.
Cybersecurity now also focuses on proactive measures. Rather than reacting to threats after they occur, modern systems aim to predict and prevent future attacks. This proactive approach includes continuous monitoring and real-time alerts. It has changed how organizations think about security, leading to more robust defenses. Businesses are investing in these advanced solutions to stay ahead.
Despite advancements, the challenges in cybersecurity continue to grow. New threats emerge regularly, requiring constant updates and improvements. Staying informed and adaptable remains crucial for individuals and organizations alike. As technology advances, cybersecurity solutions will need to keep pace, ensuring a safer digital environment for everyone.
The role of cybersecurity solutions in data protection
Cybersecurity solutions play a crucial role in protecting data. With increasing amounts of sensitive information stored online, the need for robust data protection has never been higher. These solutions use various methods to secure data against unauthorized access and breaches. Encryption, firewalls, and multi-factor authentication are commonly used. Using these tools ensures that data remains safe from cyber threats.
Encryption is one of the strongest methods for data protection. It converts data into a code to prevent unauthorized access. Only those with the correct decryption key can read the information. This method is widely used in securing sensitive information such as financial data. Even if the data is intercepted, it remains unreadable without the key.
Firewalls act as barriers between trusted and untrusted networks. They monitor and control incoming and outgoing network traffic based on predetermined security rules. This helps in blocking malicious traffic and preventing unauthorized access to systems. Firewalls are a fundamental part of any cybersecurity strategy. They ensure that only legitimate data and users gain entry.
Multi-factor authentication (MFA) adds an extra layer of protection. It requires users to provide two or more verification factors to gain access to a resource. This could be something they know, have, or are (like a password, security token, or fingerprint). By implementing MFA, the chance of unauthorized access is significantly reduced. It makes systems much harder for attackers to breach.
Organizations also use intrusion detection systems (IDS) to protect data. An IDS monitors network traffic for suspicious activity and issues alerts. It helps in identifying potential threats early and mitigating them. Here’s a table summarizing some key data protection methods:
| Method | Purpose |
|---|---|
| Encryption | Data Encoding |
| Firewalls | Network Traffic Control |
| Multi-factor Authentication | Enhanced User Verification |
| Intrusion Detection Systems | Threat Monitoring |
These cybersecurity solutions work together to create a strong defense against data breaches. Implementing them helps organizations maintain the integrity, confidentiality, and availability of their data. Effective data protection is essential for gaining and maintaining trust in the digital world.
Future trajectory of cybersecurity solutions
As technology advances, the future of cybersecurity solutions looks promising and dynamic. Emerging technologies such as artificial intelligence and machine learning are shaping new defense strategies. These technologies help in predicting and responding to threats more efficiently than ever before. They are expected to lead the way in automating security processes. This change means less manual monitoring and greater accuracy in threat detection.
The Internet of Things (IoT) is expanding rapidly, with more devices connecting online each day. Securing these devices presents unique challenges for cybersecurity experts. The future trajectory includes developing advanced protocols specifically for IoT security. These measures aim to protect vast networks from unauthorized access and malicious attacks. Here’s a look at anticipated trends:
- AI-driven Threat Detection
- Enhanced IoT Security Protocols
- Blockchain-based Security Systems
Quantum computing is another frontier impacting cybersecurity solutions. While it promises immense computational power, it also poses risks by potentially breaking current encryption methods. However, this challenge encourages the development of quantum-resistant algorithms. Adapting to quantum computing will be crucial for maintaining data security in the coming years. Businesses must stay informed about these advancements.
Privacy concerns are leading to stricter regulations on data protection across countries. Future solutions will need to comply with these evolving laws while providing robust defenses against breaches. Companies will have to balance innovation with adherence to legal standards. Users expect their personal information to be handled responsibly and securely.
The role of human expertise remains vital despite technological advancements. Cybersecurity professionals analyze complex patterns that machines may not catch immediately. Their insights guide the development and implementation of effective solutions tailored to specific needs. Teams working alongside AI can create a formidable line of defense against cyber threats.
Concluding Thoughts on Cybersecurity Solutions
Cybersecurity solutions are essential in our fast-paced digital age. They have evolved from simple antivirus programs to sophisticated systems that detect and prevent complex threats. With the integration of AI and other advanced technologies, these solutions offer enhanced protection. The continuous development in this field ensures that organizations can better safeguard sensitive information.
The future of cybersecurity is both exciting and challenging. Emerging technologies and evolving threats necessitate constant innovation and adaptation. Professionals in the field must remain agile and informed to address these challenges effectively. As we navigate this digital landscape, the collaboration between technology and human expertise will continue to be crucial for robust defense strategies.