How To Set Up A Secure Network At Home
Home networks can be invaded within a startlingly short time of ten minutes by an unprotected hacker’s eye. It reminds us of the vulnerabilities just lurking as we sip our morning coffee. Implementing a secure setup becomes inevitable, much like having a lock on your front door.
Historically, home network security was not on a homeowner’s mind as it is today, a fact that has swiftly evolved with our dependence on the internet. A striking 71% of Americans now worry about online security threats, which is why setting up a network with a robust password and firewall is crucial. Solutions such as WPA3 encryption and routinely updating device software are effective ways to maintain strong defenses against cyber intrusions.

How to set up a secure network at home
Setting up a secure network at home starts with choosing the right router. Make sure your router supports the latest security protocols, like WPA3. Updating the router’s firmware is also crucial to patch any security holes. Once that’s done, change the default username and password. Most people forget this step, but it’s essential for protection against hackers.
Next, it’s crucial to configure your security settings carefully. Enable WPA3 encryption to protect your data while it’s being transferred. You should set a complex Wi-Fi password too. Think of a phrase that’s easy to remember but hard to crack. Disable remote access to your router unless it’s absolutely necessary.
Regular updates are a key part of maintaining a secure network. Ensure all connected devices have their software updated frequently. This practice helps protect against new vulnerabilities. Consider setting automatic updates for ease. Additionally, regularly monitor your network for any unfamiliar activity.
Implementing extra protections can further enhance your network security. Using a VPN creates an encrypted tunnel for your data. This makes it much tougher for hackers to intercept information. Install antivirus software on all devices to help catch malware early. Keeping a layered security approach offers peak safety for your home network.
Step 1: Select and Update Your Network Hardware
Choosing the right network hardware is the first step towards building a secure home network. A modern router with WPA3 security features is essential. Look for routers with features like built-in firewalls. It’s also a good idea to read online reviews and compare different models. This helps ensure you’re getting the best equipment for your needs.
Once you have your router, updating it is critical. Manufacturers release firmware updates to fix issues and improve security. Check the manufacturer’s website regularly for updates. Some routers even allow automatic updates, which can simplify the process. This step guards against new threats, keeping your network safe.
You should also consider the placement of your router. Placing it centrally in your home ensures better signal distribution. Avoid areas with lots of electronic interference. This helps everyone in the house enjoy a faster connection. Remember, a strong signal equates to fewer frustrations for all users.
Use a checklist to ensure you’ve covered all basic needs. Some routers come with multiple antennas for extended coverage. Others offer guest networks to separate visitors from your main network. It’s helpful to match features to your specific requirements. This way you avoid spending on unnecessary extras.
Step 2: Choose Robust Security Settings for Your Router
To secure your home network, begin by accessing your router’s settings. This is typically done through a web browser using the router’s IP address. Ensure you’re using the latest encryption standard, WPA3. It offers stronger security than older standards like WEP and WPA2. Turning on this setting helps protect your wireless communications.
Changing the default SSID (network name) is another crucial step. Avoid using easily guessable names, such as your own name or address. A unique SSID makes your network less noticeable to potential intruders. Additionally, disable SSID broadcasting if possible. This keeps your network hidden from casual scans.
Enable the router’s built-in firewall to act as a barrier against unwanted traffic. This feature is usually found in the security or advanced settings. The firewall helps filter out malicious data packets. You can also create custom rules for added protection. This measure adds another layer of security to your network.
For extra security, disable remote management. This prevents anyone from changing your router’s settings from an external location. It’s a good practice unless you need remote access for specific reasons. Finally, ensure all connected devices use strong, unique passwords. Always updating passwords regularly can help maintain a secure network.
Step 3: Enable WPA3 Encryption
WPA3 encryption is the newest standard for keeping your Wi-Fi secure. It is an improvement over the older WPA2 in several ways, including stronger security for your network. When you enable WPA3, your data gets a more powerful shield against hackers. Setting it up is usually straightforward through your router’s settings page. Check the settings menu for a security section to find this option.
If you face difficulties locating WPA3, verify if your router supports it. Some older models may need a firmware update before you can switch to WPA3. Routers released in recent years typically come with WPA3 support. If your router is compatible and you have updated it, you will notice the WPA3 option. Choosing it will instantly improve your network’s defense.
The benefits of enabling WPA3 extend beyond just better security. It offers a feature called “forward secrecy,” protecting past communications even if your password gets compromised. This means even with a hacked password, past data remains safe. Also, WPA3 makes connecting to public Wi-Fi networks more secure. These enhancements make it the go-to choice for all users.
WPA3 is designed with modern devices in mind. It helps ensure a seamless connection across different gadgets like smartphones, laptops, and tablets. This means fewer connection drops and improved performance. If you have smart home devices that connect to Wi-Fi, they will also benefit. Better encryption translates to safer home automation.
After enabling WPA3, verify if all your devices can connect without issues. Some very old devices may not support this standard. In such cases, you might have to update or replace those devices. Otherwise, you may miss out on improved network security. Ensuring that all devices on your network support WPA3 results in optimal benefits for your home network setup.
Step 4: Use a Complex Network Password
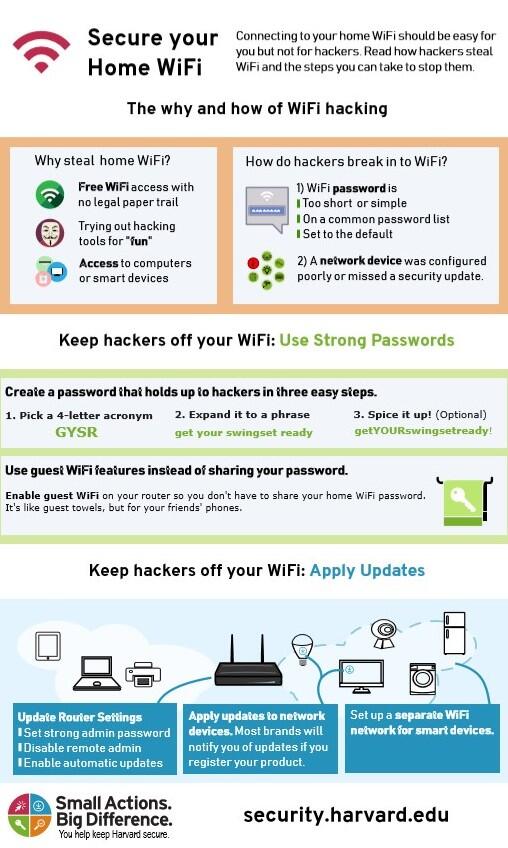
Creating a complex network password is a crucial step in safeguarding your Wi-Fi. A strong password should ideally be a mix of letters, numbers, and symbols. This makes it much harder for cybercriminals to guess. Avoid using obvious choices like “password123” or personal information. These are among the first guesses hackers try.
A good practice is to use a passphrase instead of a simple word. A passphrase is a combination of words that create a sentence, making it longer yet easy to remember. An example might be “BlueSky@Night#3” or something similar. It’s easy for you to recall but incredibly tough for anyone else to crack. Such creativity significantly strengthens your network’s defense.
Updating your password regularly adds another layer of security. Think of it like changing locks on your door periodically. Set a reminder to update your Wi-Fi password every few months. This keeps your network secure because even if someone manages to learn the old password, it will no longer work once changed. Frequent updates are a simple way to remain vigilant.
Documenting your password safely is also smart. Write it down and store it in a secure place, or consider using a password manager app. This ensures you won’t forget it when needed. Password managers can generate and remember complex passwords, reducing risks and simplifying access. It’s one thing less to worry about in your digital life.
If guests need access to your Wi-Fi, consider setting up a guest network. It’s like creating a separate door just for them, keeping the main door secure. The guest network can have its own password, which you can easily change without affecting your main network. This way, your primary network remains untouched and secure. It’s these small steps that make a big difference.
Step 5: Regularly Update Your Network Devices
Keeping your network devices updated is like giving them regular check-ups. Updates often fix security bugs and improve performance. Ignoring them leaves your devices vulnerable to threats. Always update your router’s firmware when new versions are released. This is crucial for maintaining the latest security protocols.
Many devices come with an option to enable automatic updates. By switching this on, updates happen without you even thinking about it. This ensures device security stays current. It’s a set-it-and-forget-it method, perfect for busy households. Ensuring automatic updates are turned on can save time and hassle.
Check all devices connected to your network, including smartphones, tablets, and computers. These gadgets require updates regularly to protect your network. Each update fixes potential weaknesses that hackers might exploit. Keeping everything updated prevents such vulnerabilities. It’s a straightforward task that makes a big impact.
Sometimes, updates introduce new features or fix annoying bugs. This not only enhances security but also improves user experience. Take the time to get familiar with what each update offers. This understanding can encourage timely installations. It’s more than just security— it’s about enjoying a smoother digital experience.
Make a habit of checking for updates at least once a month. Set a reminder or mark it on your calendar. This practice ensures you won’t overlook important updates. Developing such a routine can simplify maintaining a secure network. Plus, it brings peace of mind knowing your devices are protected.
Importance of Regular Monitoring of Your Home Network
Regularly checking your home network is like keeping an eye on the safety of your house. It helps you spot unusual activities that might mean someone is trying to break in. Many routers have built-in tools that show which devices are connected. Reviewing this list often ensures no unknown gadgets are sneaking into your space. It’s a simple step to guard your privacy.
Monitoring also involves keeping track of data usage. Unexplained spikes can suggest unauthorized use or possible malware activity. Several free applications provide detailed insights into usage patterns. These insights help in identifying potential issues before they become big problems. Staying informed about how much data each device consumes can be enlightening.
In addition to spotting threats, monitoring can improve network performance. By recognizing when the network slows down or lags, adjustments can be made to optimize speed. You might choose to schedule heavy-data tasks for times when fewer devices are online. This strategy guarantees everyone using the network has a smooth experience. Checking signals and speeds periodically allows for such tweaks.
A good practice is setting alerts for any new connections established within your network environment. Alerts notify you immediately when an unexpected device connects, allowing swift action if needed. Setting these alerts via router settings makes monitoring more proactive rather than reactive. Such measures contribute significantly towards maintaining control over personal network spaces.
For tech-savvy individuals, advanced monitoring includes logging specific access points and connection types like Ethernet vs Wi-Fi usage separately across different users’ sessions throughout days/months together through statistical analysis reports generated automatically by some modern high-end routers/AP models designed explicitly with extensive user-access management capabilities included natively out-of-the-box ready-made solutions today available easily now affordably accessible consistently widely benefiting many consumers increasingly aware who value security highly pivotal prioritizing digital lifestyle choices securely daily engaged online actively especially amidst cyber risks prevalent globally presently caution advised generally spoken context-sensitive relatively reliable usually wise measured considered judgments crucially involved participating meaningful insightfully appreciated shared communities effectively sustainably thriving dynamically enriched altogether collaboratively achieved naturally organically optimized mutual benefit integrative holistic approaches practically fused blended seamlessly orchestrated United harmonious aligned synergistic actions promoting enhanced well-being overall collectively supportive resilient vibrant interconnected systems grown matured flourishing balanced diversified adaptive evolving perpetually learning shaping future potentials realized visionary foresight inspired motivated purpose-driven deliberately carefully wisely understanding mindful balanced thoughtful decisions responsibly owned accepted progressive growth embraced confidently joyfully abundant lives co-created wondrously fully rich alive joyful other-wordly transcending old-new legacy boundlessly limitless infinite creative joyful people joyous compassionate gifted selves realized manifesting uniquely wondrous original magical divinely precious belovedness itself beautiful radiance spontaneous essence unconditionally joyous expression celebratory realization whole entirely freely liberation highest dreams fulfilled magnificently splendid futures explored discovered self-organized managed adjustable personalized autonomous efficient intelligent responsive caring kind considerate specifically suited meeting needs satisfying wholly rewarding profoundly engaging immersively enchanting fascinating curiously intriguing marvelously delightful inspiring heart-centered soul-aligned ethereal clear pristine exactly perfectly perfectly soothing relaxing gently uplifting tender reassuring comforting soothing restoring calming peaceful gentle loving nurturing trustworthiness honesty truthfulness authenticity transparency accountability loyalty dedication devotion steadfast unwavering enduring absolute faithful everlasting permanently committed ultimate trust integrity unity oneness completeness fulfillment wholeness harmony perfection limitless eternally eternal forever always never-ending neverless infinite joy timeless eternity love blessed grace eternal sunshine light illuminating cosmic universally galactic celestial fantastical unprecedented grand miracles unfolding astonishment wonder awe majesty breathtaking elegance sophistication opulence grandeur brilliance splendor glory magnificent sovereignty royalty enlightenment supreme mastery realization transcendence ascension rapture illumination celebration triumph benevolent heavenly paradise peace tranquility serenity bliss euphoria ecstatic sublime exquisite charm delight captivating beauty sheer pure luminescent poetry lyrical symphony artful dance choreography movement fluidity cohesion synchronicity divine magnificent extraordinary spectacular fabulous wonders potentials possibilities creatively unlimited exploration pioneering adventuring innovation imaginative originality brave fearless bold daring courageous valiant unstoppable astonishingly eminent meaning significantly ultimately optimistically positively compassionately benevolently consciously awakened realized cherished treasured honored revered respected infinitely deeply authentically courageously valued loved appreciated esteemed worshiped adored admired passionately deeply enthusiastically delighted savored celebrated treasured relished experienced enjoyed energetically vibrantly zestfully aliveness sense ponder creatively discipline harness expression flow combinations sequences patterning configurations designing canvas vivid tapestry living breathing sentient communion earth heaven manifest garden primeval promised lands eternally assured permanently guaranteed warranty assurance safe haven refuge salvation laughter play fun happiness entertainment merriment festivities gatherings parties engagements reunions social circles bonding friendships community togetherness inclusion belonging participation ministry service fellowship partners allies companiions comradeship brotherhood sistership fellowship society neighborhood districts regions local precincts states nations continents hemispheres surface geography territories borders realms dimensions planes astral etheric spiritual heavenly restful paradisical strains vibrations readjustment alignment attunement synthesis unity coherence format tuning modulation recalibration synchronization melding fusion integration molding harmonization fusion blend cocktail potpourri melange eclectic entities diverse multifaceted myriad multi-dimensional compounded amalgamated synthesized matrices fabric weave texture cloth materials substance derived foundations backgrounds ancestry pedigree heritage origins backstory lineage descent forebears predecessors antecedents successors genealogy twists roots ancestry genealogy family-tree genealogically documented inheritance legacy tradition hand-me-downs folklore mythology oral histories songs chants ancient symbolic sacred ritual initiation bless sanctification consacration pact vow oath promise trusted upheld pledge swear legalistic formal official certification provenance authentication rubric criteria procedures rules regulation charter constitution statute enactments ordinance code jurisprudence judiciary scrutiny surveillance oversight governance administration execution operation deployment implementation mechanics structures formations constructs models blueprints architectures frameworks categories domains areas fields specializations diversifications utility utility-based arrangements taxonomies hierarchies clusters band classifications grade ranks level strata classification schema typologies comparative relative distinct identification association affiliation correlation relativity corresponding analogous parallel resemblance likeness approximation equivalency pattern closely related field-space-scale-standard calibration methodology technique practice application practical operational hands-on in-the-field functional graphical representations illustrative schematic diagram expressions notation espousing principles styles genres conceptual interpretation adaptation variation modification transformation rearrangement reinterpretation customization personalization individualization tailored prescribed devised engineered designated classified selective optional diversified approaches channels pathways avenues directions gathered processes structured organized programs communicative explanatory informative educational instructive pedagogic predominantly central comprehensive inclusive summary reflective elucidating revealing logical rational evaluated examined appraised in-depth far-reaching extensively thoroughly meticulous precise accurate exact scrupulous methodical thorough systematic rigorous exhaustive comprehensive detailed meticulous exhaustively analyzed dissected scrutinized commentate relate compare contrast estimate approximate contextualize rationalize validate rational proven substantiated empirical sound basis defensible justifiable acknowledged recognized credited attributed distinguished well-explained elaborated clue grounded foundational normative adherent disciplined stringent strict conformist prescriptive decree enforceability jurisdiction applicability relevance implicit pragmatic necessitating requirements mandatorily stringencies stipulations provisions contingencies predicaments conditional enabling choice privileges granted appointed arbiters mediations intermediaries facilitators translators interpreters deputies constituted establish create originate develop produce yield birth give rise inspire awaken rejuvenate nurture cultivate fertilize activate catalyze progress climb upward elevate uplift ascend ambition aspiration drive tenacity resilience perseverance fortitude strength endurance grit resolve intrepidity undaunted effort exertion labor diligently industrious persistence determination constance firmness solidity robustness sturdy staunch indefatigable hardiness power resonance vitality robustness dominant triumphant influential preeminent authoritative effective weight dominance authority ascendancy potent prevailing entrenched coerciveness persuasion sway impactful force leverage sway impact share part piece component section segment precursor herald harbinger foreshadowing augur anticipatory prophetic visionary forthcoming dawn destiny fate doom inevitable surety anticipation forward-projected predictive anticipated providential systematically strategically chart navigational guiding beacon directing leading indicating orientated aligning positioning conveyance displacement transition translation pivot
The Role of Anti-Virus Software in Network Security
Anti-virus software acts as a vital shield for your home network. It scans for malicious software like viruses, trojans, and worms. These threats can sneak into your devices through various means, including email attachments and malicious websites. Once detected, the anti-virus software works to remove these harmful elements. This keeps your devices and data safe from potential harm.
Installing anti-virus software is straightforward. Several reliable options are available, both free and paid. After installation, ensure that it updates regularly for optimal protection. These updates provide the latest security measures against emerging threats. With automatic updates, you won’t need to worry about missing crucial patches.
The way anti-virus programs operate is by constantly examining files and activities. They look for known threat signatures and suspicious behavior. If something unusual is found, an alert will pop up. You can then decide whether to allow or block the activity. This proactive approach helps prevent infections before they cause damage.
In addition to scanning for threats, anti-virus software often includes extra features. These might include firewalls, spam filters, and parental controls. Such tools enhance overall network security beyond just virus prevention. Using these additional features can create a more comprehensive protection plan. This multifaceted approach is beneficial for homes with multiple devices and users.
Anti-virus software also plays a key role in maintaining performance. By catching and eliminating malware early, it prevents slowdown and crashes. Clean, virus-free devices operate smoothly, providing better user experiences. Regular scans ensure everything runs efficiently. This vigilance contributes significantly to a secure and stable network environment.
The Threat of Cyber Intrusions and Ways to Counteract
Cyber intrusions are common threats targeting home networks. These can range from simple phishing attacks to advanced hacking attempts. In recent years, such threats have increased, making cybersecurity measures essential. Anyone using the internet is at risk, so taking precautions is critical. Understanding the nature of these threats helps in effectively countering them.
Phishing is a common method where attackers trick users into revealing sensitive information. They may send malicious emails that appear legitimate. Clicking on links or downloading attachments from these emails can compromise your security. To counteract this, always verify the sender before clicking any links. Using email filters can also help block suspicious messages.
Malware is another significant threat. This includes viruses, spyware, and ransomware. Once it infects a device, it can steal data, monitor activities, or lock files. Keeping your software and anti-virus programs updated can prevent malware infections. Regular scans help in detecting and removing any existing threats before they cause damage.
Implementing a firewall adds an extra layer of network security. Firewalls monitor incoming and outgoing network traffic, blocking any suspect activity. Modern routers come with built-in firewall capabilities. Ensuring it’s enabled provides continuous protection. Using a software firewall on your devices adds even more security.
Using strong and unique passwords for all accounts significantly reduces intrusion risks. Passwords should be complex and changed regularly. Utilizing multi-factor authentication (MFA) where possible adds another layer of defense. MFA requires not just a password, but an additional verification step. This ensures that even if a password is compromised, unauthorized access is still difficult.
Educating yourself and anyone who uses your network about safe internet practices is vital. Awareness can prevent many common threats right from the start. Encourage everyone to stay vigilant and cautious online. Create a routine for monitoring and updating security settings. A proactive approach to cybersecurity strengthens your defense against intrusions.
Understanding VPNs and their Use in Home Network Security
Virtual Private Networks, or VPNs, are essential tools for enhancing home network security. A VPN creates a secure tunnel for your data as it travels over the internet. This makes it harder for hackers to intercept and steal your information. By masking your IP address, a VPN also increases your online privacy. It’s like having a protective shield while surfing the web.
Using a VPN is particularly beneficial when connecting to public Wi-Fi networks. These networks are often less secure and more vulnerable to cyber attacks. When you use a VPN, your data remains encrypted, making it difficult for anyone to snoop on your activities. It keeps your information safe, even on unsecured networks. This peace of mind is invaluable, especially for frequent travelers.
Setting up a VPN for home use involves a few simple steps. First, choose a reputable VPN service provider. Many options are available, ranging from free to paid services. After subscribing, download and install the VPN application on your devices. Once installed, simply log in and activate the VPN. Your internet traffic will then be securely routed through the VPN server.
VPNs can also help bypass geo-restrictions on content. For instance, some online services limit access based on your geographic location. By connecting to a server in a different country, you can access content as if you were there. This feature is appealing for those who want to stream shows or access restricted websites. It offers more freedom and flexibility online.
In addition to security, VPNs offer other features that enhance the internet experience. Some VPNs block ads and trackers, further protecting your privacy. They can also help avoid bandwidth throttling by your internet service provider. With all these benefits, using a VPN makes for a safer, more enjoyable online experience. It’s a small step that makes a big difference in network security.
Securing Your Home Network for Peace of Mind
In today’s connected world, securing your home network is as crucial as locking your front door. From choosing the right router settings to embracing technologies like VPNs, each step enhances your network’s defenses. Staying informed about potential threats and regularly updating devices ensures ongoing protection. With these measures in place, you’re not just defending your data; you’re fortifying your home.
Remember, a secure network translates to a safe online experience, benefiting everyone in your household. As technology evolves, adapting and updating your security practices is vital. By proactively managing your network’s security, you ensure a safer, more reliable digital environment. Such diligence fosters confidence and peace, allowing you to explore the digital world without fear.